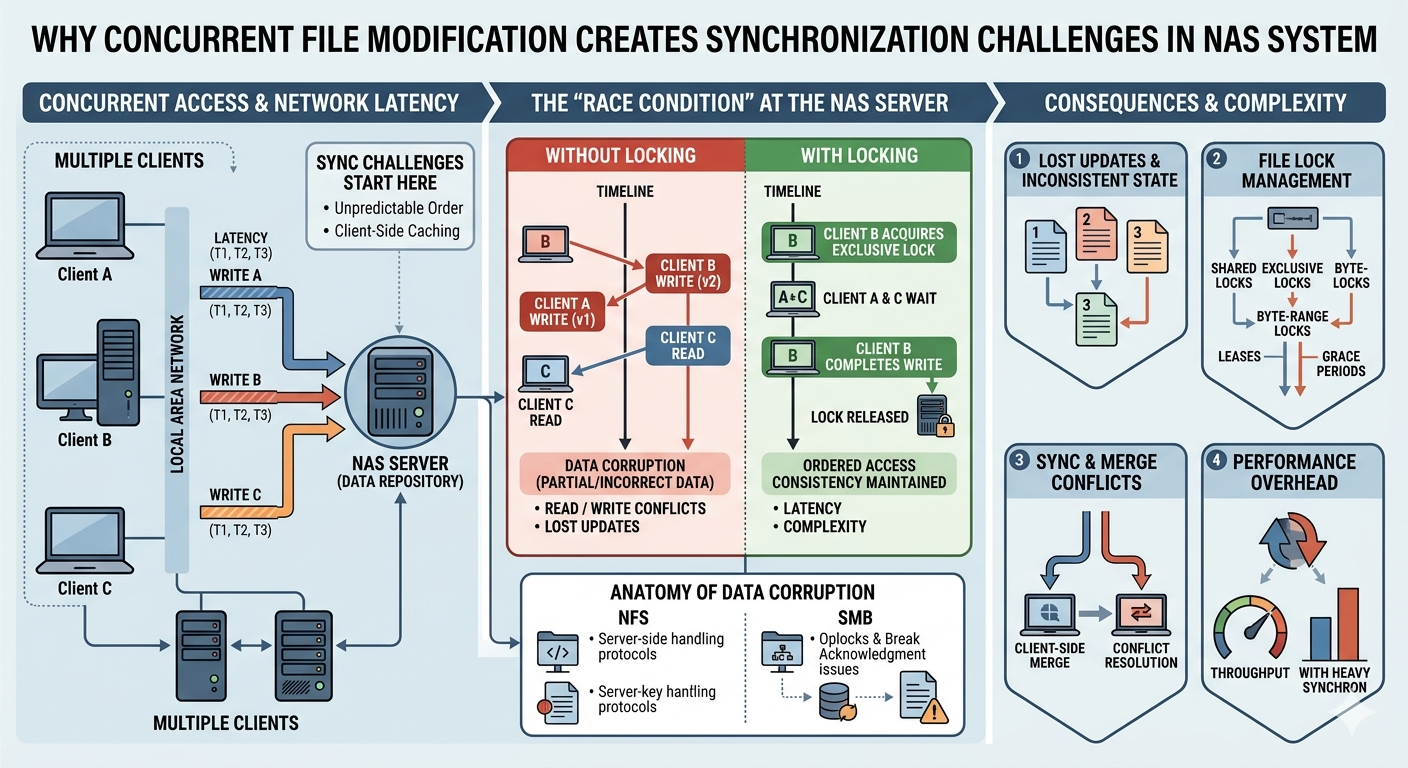
Network-attached storage architectures fundamentally rely on coordination protocols to manage multiple client requests across shared storage pools. When multiple users or automated processes attempt to read, write, or modify the exact same file simultaneously, the infrastructure must rapidly determine which operation takes precedence. If these concurrent operations are not strictly managed, the resulting overlap leads to severe data corruption, metadata inconsistencies, and application failures.
Understanding how a Nas System handles these simultaneous requests requires examining the underlying communication protocols and file system architectures. Traditional network protocols, such as Network File System (NFS) and Server Message Block (SMB), utilize specific locking mechanisms to arbitrate access. When an application opens a file, the protocol requests a lock from the storage controller. This lock signals to all other clients on the network that the file is currently in use, preventing secondary modifications until the initial process releases its hold.
However, network latency, application caching, and distributed computing models complicate this seemingly straightforward process. In environments supporting thousands of active connections, an Enterprise nas must process locking requests in milliseconds to prevent workflow bottlenecks. When the locking mechanisms fail or when applications ignore protocol-level locks, concurrent file modification creates significant synchronization challenges that jeopardize the integrity of the entire storage repository.
The Mechanics of File Locking and Synchronization
The primary method for preventing concurrent file modification relies on file locking. When a user opens a document stored on a Nas System, the client machine communicates with the storage server to establish a lock state. Depending on the specific protocol configuration, this lock can be exclusive, preventing any other user from reading or writing, or shared, allowing read-only access while blocking write operations.
Opportunistic Locks and Caching
Modern protocols implement advanced features like opportunistic locks (oplocks) or client-side caching to improve performance over high-latency networks. A client granted an exclusive oplock can cache file modifications locally, delaying the actual data transmission to the central Nas System. While this significantly reduces network traffic and improves application responsiveness, it creates a synchronization vulnerability. If a second client requests access to the same file, the server must recall the oplock, forcing the first client to flush its local cache back to the storage array before granting access to the second user. If a network disruption occurs during this recall phase, the synchronization state breaks, leaving the file in an inconsistent or locked state.
Metadata Management Bottlenecks
Every file modification requires a corresponding update to the file system's metadata. This metadata records file sizes, access timestamps, and physical block locations on the storage media. In a large-scale Enterprise nas, thousands of concurrent file modifications generate a massive volume of metadata transactions. The storage controller must serialize these metadata updates to prevent corruption of the directory structure. If two processes attempt to append data to a single log file concurrently, the metadata must accurately reflect the exact sequence of blocks written. Failure to synchronize these updates results in orphaned blocks or overwritten data segments, compromising the file's structural integrity.
Differentiating File-Level and Block-Level Storage
The synchronization challenges associated with concurrent access change significantly depending on the storage architecture deployed. Traditional network-attached storage operates at the file level, meaning the storage controller manages the file system, directory hierarchy, and access permissions. The client simply requests specific files, and the storage array handles the underlying block allocation.
The Role of an ISCSI NAS Architecture
Conversely, an ISCSI NAS operates using block-level storage protocols over a standard IP network. Instead of presenting a formatted file system to the client network, an ISCSI NAS presents raw logical unit numbers (LUNs). The client machine connects to these LUNs and formats them with its own local file system, such as NTFS or ext4. Because the client operating system believes it is interacting with a direct-attached local disk, it assumes total control over file locking and metadata management.
This architectural shift introduces unique synchronization hazards. If multiple distinct servers connect to the same target LUN on an ISCSI NAS without using a specialized cluster-aware file system, they will independently attempt to manage the storage volume. Server A will write data and update its local understanding of the metadata, while Server B remains entirely unaware of these changes. When Server B attempts to write to the same LUN, it will overwrite the data placed by Server A, causing immediate and catastrophic data loss.
Clustered File Systems for Block Storage
To safely share a target volume on an ISCSI NAS across multiple host servers, administrators must implement cluster-aware file systems, such as VMware's VMFS or Windows Cluster Shared Volumes (CSV). These specialized file systems introduce a distributed lock manager (DLM) that coordinates access across the network nodes. Before any server can modify a file or update the underlying metadata on the ISCSI NAS, it must acquire a cryptographic lease from the cluster coordinator. This ensures that even at the raw block level, concurrent modifications are strictly serialized and synchronized.
Scaling Challenges in High-Performance Environments
As organizations expand their data footprints, the complexity of managing concurrent modifications scales exponentially. An Enterprise nas must support highly available, active-active node configurations where storage controllers are distributed across different physical locations. In a scale-out architecture, a single file might be striped across multiple independent storage nodes to maximize throughput.
Distributed Lock Management
In these distributed environments, a centralized locking mechanism becomes a severe performance bottleneck. Therefore, an Enterprise nas relies on distributed lock management. Instead of a single master controller handling all access requests, the locking authority is distributed dynamically among the cluster nodes based on which node holds the majority of the file's data blocks. This requires continuous background communication between the storage controllers to maintain a unified state table.
When concurrent file modifications occur in a distributed Enterprise nas, the system must navigate the split-brain scenario. If the inter-node communication network fails, two distinct storage controllers might independently grant exclusive write locks to the same file to different clients. To prevent this, enterprise architectures utilize quorum disks and fencing mechanisms. If a node loses connection to the cluster majority, it immediately halts all input/output operations, sacrificing temporary availability to guarantee strict data synchronization.
Managing Storage Integrity Across Distributed Environments
Mitigating the synchronization challenges of concurrent file modification requires strict adherence to architectural best practices. Storage administrators must carefully evaluate the specific workload profiles of their applications before provisioning storage resources. Applications requiring massive, uncoordinated concurrent writes to shared databases often perform poorly on standard file-level protocols and require dedicated block-level configurations.
By understanding the distinct locking mechanisms of an ISCSI NAS versus traditional file-sharing protocols, infrastructure teams can select the appropriate clustering software to prevent metadata overwrites. Furthermore, implementing an Enterprise nas with robust distributed lock management and quorum fencing ensures that data integrity is maintained even during severe network partition events. Thorough configuration of these underlying protocols ensures that every single modification is accurately recorded, sequenced, and committed to the storage array without conflict.