Shared infrastructure requires continuous, uninterrupted connectivity to function properly. When multiple virtual machines, applications, and users rely on a single physical framework, a single point of failure can disrupt entire operations. Hardware malfunctions, severed cables, or switch misconfigurations can instantly sever the connection between compute nodes and data repositories. Left unmanaged, these link failures result in application downtime, corrupted databases, and significant financial losses.
Understanding how systems isolate these disruptions is critical for IT professionals. Robust architecture ensures that when a path goes down, the rest of the network remains unaffected. This blog explains the precise mechanisms Network Storage Solutions use to manage link failure isolation across shared infrastructure. You will learn about redundancy protocols, the importance of NAS Storage configurations, and how NAS Security protocols protect data integrity during network routing events.
The Architecture of Shared Storage Environments
Shared infrastructure pools computing, network, and storage resources to maximize hardware utilization. In these environments, administrators frequently deploy NAS Storage arrays to handle file-level data access for multiple clients simultaneously. Because data requests constantly traverse the network, the physical and logical links connecting the servers to the storage arrays must be highly resilient.
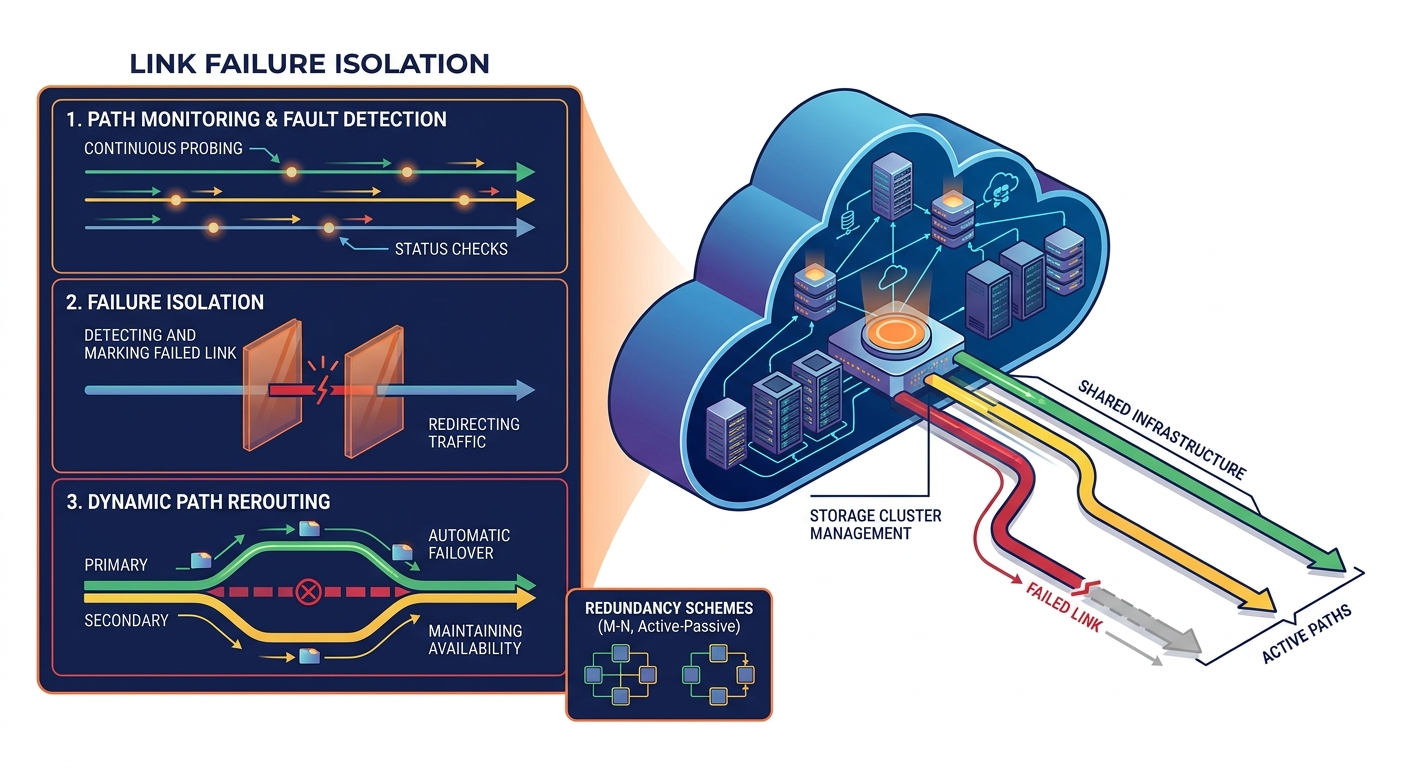
Network Storage Solutions operate on the principle that hardware components will inevitably fail. To combat this, architects design systems with no single points of failure. This involves redundant network interface cards (NICs), multiple network switches, and diverse cabling paths. When an application requests a file from NAS Storage, the data packets travel across these physical links. If one link fails, the system must immediately recognize the drop and isolate it, ensuring traffic seamlessly reroutes through available secondary paths without dropping the connection.
Core Mechanisms for Link Failure Isolation
Isolating a failure means preventing a localized issue from cascading across the broader network. Network Storage Solutions achieve this through several layered networking protocols and software configurations.
Multipathing Software
Multipathing is a fundamental technique for link failure isolation. It establishes multiple physical connections between the server and the storage array. The multipathing software monitors the health of all available paths. If a cable is unplugged or a switch port dies, the software detects the loss of the signal. It instantly isolates the failed link by removing it from the active routing table.
Traffic is then dynamically shifted to a standby or active secondary path. Because this happens at the driver level, the application requesting data from the NAS Storage remains completely unaware of the physical disruption. The operation continues with minimal latency spikes.
Link Aggregation and LACP
Link Aggregation Control Protocol (LACP) bundles multiple physical ports together to form a single logical channel. This provides both increased bandwidth and automatic fault tolerance. If one physical link within the bundle fails, LACP automatically isolates that specific link. It redistributes the data traffic across the remaining operational links in the bundle. Network Storage Solutions rely heavily on LACP to provide seamless failover, ensuring that shared infrastructure maintains a steady flow of data even under degraded conditions.
Protecting Data Integrity During Failover
Link failures are not just availability issues; they are potential security and data integrity risks. When traffic reroutes, it must do so securely. This is where NAS Security becomes a primary focus.
Defending Against Malicious Disruptions
Not all link failures are accidental. Malicious actors sometimes trigger denial-of-service attacks against specific network segments to force a failover, attempting to route traffic through less secure secondary paths. Robust NAS Security policies ensure that all network paths—both primary and secondary—enforce the exact same authentication and encryption standards. Network Storage Solutions must validate that any newly established connection during a failover event complies with the organization's zero-trust architecture.
Preventing Split-Brain Scenarios
In high-availability clusters, a link failure can sometimes sever the communication between two active storage controllers. If both controllers believe the other has failed, they might both attempt to take ownership of the NAS Storage resources. This is known as a split-brain scenario, and it can lead to severe data corruption.
To prevent this, Network Storage Solutions utilize isolation techniques like SCSI-3 Persistent Reservations or quorum tie-breaker disks. These mechanisms ensure that only one controller retains write access to the NAS Storage, physically isolating the disconnected node until the link is restored. Proper NAS Security configurations mandate these locking mechanisms to preserve data consistency.
Implementing Resilient Network Storage
Designing a resilient infrastructure requires a systematic approach to network configuration. Administrators must ensure their Network Storage Solutions are properly tuned to detect and isolate failures rapidly.
First, configure hardware redundancy from the ground up. Use independent network switches and distinct power sources for your core infrastructure. Second, implement comprehensive monitoring tools. These tools should alert administrators the moment a link drops, allowing for hardware replacement while the redundant paths handle the traffic.
Third, regularly audit your NAS Security settings. Conduct failover drills to verify that access controls and encryption protocols remain active when traffic shifts to backup links. By integrating stringent NAS Security practices with robust hardware redundancy, organizations can build NAS Storage environments that withstand localized hardware failures without compromising overall performance.
Securing Continuous Access in Shared Environments
Hardware components will fail, but those failures do not have to impact end users. By utilizing advanced multipathing, link aggregation, and strict access controls, modern Network Storage Solutions isolate disruptions quickly and effectively. Maintaining highly available NAS Storage requires continuous monitoring and a commitment to redundant architecture.
To ensure your shared infrastructure is fully protected, review your current routing protocols and failover testing schedules. Evaluate your existing NAS Security policies to confirm that data remains protected, regardless of which physical path it travels. Implementing these systematic controls will safeguard your critical data against unpredictable hardware events.