Network Attached Storage (NAS) architectures frequently serve heterogeneous client environments. Windows clients natively utilize the Server Message Block (SMB) protocol, while Linux and UNIX environments rely on the Network File System (NFS) protocol. When disparate operating systems request access to the exact same file infrastructure, maintaining data consistency becomes a complex engineering challenge.
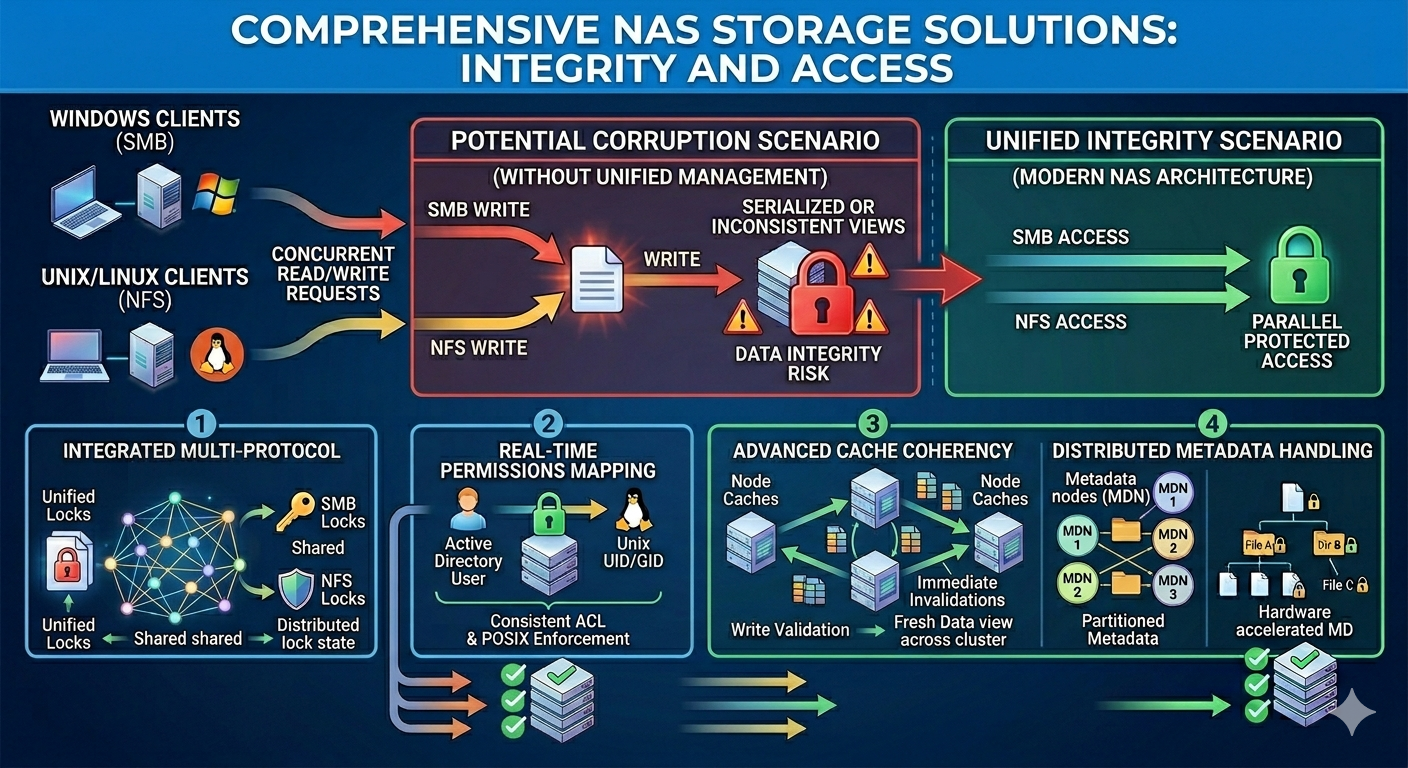
Simultaneous multi-protocol access occurs when an SMB client and an NFS client attempt to read, write, or modify a shared file at the same time. Without strict arbitration, these concurrent operations will result in race conditions, overwritten changes, and silent data corruption. Enterprise IT administrators must understand exactly how their storage infrastructure manages these collisions to prevent catastrophic data loss.
This article explains the internal mechanisms that modern NAS storage solutions utilize to resolve concurrent multi-protocol requests. You will learn how file locking protocols interact, how security identifiers translate across operating systems, and the specific methods NAS Systems employ to guarantee strict data integrity at the storage controller level.
The Architecture of Multi-Protocol Collisions
To understand how data integrity is maintained, administrators must first examine how SMB and NFS fundamentally differ in their architectural design and state management.
Stateful vs. Stateless Protocols
SMB is inherently a stateful protocol. The storage server maintains a continuous record of all open files, active sessions, and client locks. If a network connection drops, the server knows exactly which resources were locked and can manage them accordingly.
Historically, NFS (specifically NFSv3) was designed as a stateless protocol. The server processed each read or write request independently without tracking the ongoing state of the client's file access. While the Network Lock Manager (NLM) was introduced as a sideband protocol to handle locks, it lacked the integrated statefulness of SMB. NFSv4 addressed this by incorporating stateful locking directly into the core protocol. However, many enterprise environments still operate mixed NFSv3 and NFSv4 environments alongside SMB.
The Risk of Concurrent Modification
When an SMB client opens a document to edit, the Windows operating system requests a lock to prevent other users from making changes. If an NFS client attempts to write to that same file simultaneously, the NAS controller must recognize the SMB lock and deny the NFS write request. If the storage system fails to translate the lock state between the two protocols, the NFS client might overwrite the SMB client's changes. This scenario destroys data integrity.
Cross-Protocol Locking Mechanisms
Advanced NAS storage solutions solve the concurrent access problem by implementing a unified, cross-protocol locking manager at the file system level.
Unified Lock Managers
Instead of maintaining separate lock databases for SMB and NFS, enterprise NAS Systems utilize a centralized lock manager integrated directly into the underlying file system. When a client requests a lock, regardless of the protocol, the request is registered in a single state table.
If an SMB client requests an exclusive write lock, the centralized lock manager records this transaction. When a subsequent NFS request arrives for the same file, the NFS daemon queries the central lock manager, discovers the existing SMB lock, and returns a lock denial to the Linux client. This unified approach guarantees that state transitions are visible across all supported protocols instantly.
Oplocks and Delegations
Performance optimization adds another layer of complexity to data integrity. SMB utilizes Opportunistic Locks (Oplocks), allowing a client to cache file data locally to reduce network latency. NFSv4 utilizes a similar concept known as Delegations.
If a Windows client holds an exclusive Oplock and is caching writes locally, and a Linux client suddenly requests read access via NFS, the NAS storage solutions must immediately intervene. The storage controller sends an oplock break request to the Windows client, forcing it to flush its cached data back to the server. The NAS controller suspends the NFS read request until the Windows client completes the flush. Once the data is synchronized on the physical disks, the NAS grants the NFS read request. This precise sequence guarantees that the Linux client reads the most current data without compromising the Windows client's caching benefits.
Advanced Metadata and Permission Mapping
Data integrity extends beyond file locking; it also encompasses strict enforcement of security protocols. SMB and NFS utilize completely different access control models.
SIDs vs. UIDs
Windows environments identify users and groups using Security Identifiers (SIDs). UNIX and Linux environments use User Identifiers (UIDs) and Group Identifiers (GIDs). For a NAS to authorize file access securely, it must seamlessly translate these identifiers.
NAS Systems solve this through identity mapping services. By integrating with Active Directory (AD) and Lightweight Directory Access Protocol (LDAP) servers, the NAS builds a translation table. When a Linux user attempts to access a file created by a Windows user, the NAS consults the mapping table to determine if the UID corresponds to an authorized SID.
ACLs vs. POSIX Permissions
File permissions present a similar translation hurdle. Windows relies on highly granular Access Control Lists (ACLs), which can specify intricate rules for file inheritance and specific user rights. Traditional NFS relies on POSIX mode bits (Read/Write/Execute for Owner/Group/Everyone), which are far less granular.
When an NFS client attempts to modify a file secured by a Windows ACL, the NAS controller dynamically calculates an equivalent POSIX permission set to present to the NFS client. However, the NAS strictly enforces the underlying Windows ACL. If the NFS client attempts an operation that the POSIX bits appear to allow, but the ACL explicitly denies, the NAS rejects the request. This preserves the strict security posture required for enterprise data integrity.
Frequently Asked Questions
Do all NAS devices support simultaneous multi-protocol access?
No. Entry-level and consumer-grade NAS devices often support both SMB and NFS, but they partition the protocols into separate volumes or datasets. True simultaneous access—where both protocols can read and write to the exact same file directory concurrently—requires enterprise-grade lock management and unified namespace architecture.
How does NFSv3 handle locking compared to NFSv4?
NFSv3 relies on an external daemon called the Network Lock Manager (NLM). This process is separate from the primary NFS daemon and can sometimes fall out of sync during network disruptions. In NAS systems, NFSv4 integrates file locking directly into the core protocol, making it stateful and significantly more reliable when interacting with a unified cross-protocol lock manager.
Can byte-range locking be enforced across protocols?
Yes. High-end NAS storage solutions support byte-range locking, allowing clients to lock specific segments of a file rather than the entire file. The centralized lock manager maps the requested byte offsets regardless of whether the request originates from an SMB or NFS client, preventing localized data corruption within large database files or virtual machine images.
Architecting Your NAS for Reliable Concurrent Access
Maintaining data consistency across mixed operating system environments requires careful architectural planning. Relying on basic file sharing protocols without a centralized lock manager invites data corruption. By understanding how cross-protocol locking, identity mapping, and dynamic ACL translation function under the hood, administrators can deploy storage environments that safely support diverse workloads.
Audit your current storage infrastructure to determine how it handles simultaneous SMB and NFS requests. Review your identity mapping configurations in Active Directory and LDAP to ensure strict UID to SID translation. Consult your storage vendor's technical documentation to verify that their unified lock manager fully supports your specific applications and workload requirements.