Ransomware attacks have evolved from simple opportunistic encryption scripts into highly sophisticated, targeted campaigns designed to cripple enterprise infrastructure. Threat actors specifically map out network topographies to locate critical data repositories, directly compromising backup archives to eliminate the possibility of restoration. This shift in adversary tactics necessitates a fundamental redesign of data protection strategies, moving away from standard replication and focusing heavily on hardware-level and file-system-level defenses.
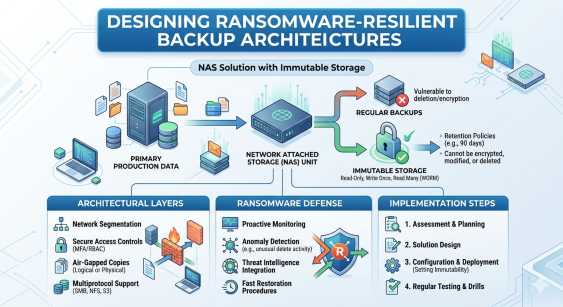
At the center of this defensive posture is the implementation of immutability. By engineering backup architectures that physically or logically prevent data modification, organizations can guarantee recovery even after a catastrophic breach with elevated privileges. Network-attached storage infrastructure must be hardened to act as an unassailable vault rather than a simple file share.
This guide details the technical requirements and architectural frameworks necessary for designing highly secure NAS environments. By implementing robust access controls, air-gapped principles, and advanced cryptographic validation, systems administrators can effectively neutralize the threat of lateral ransomware movement within their backup networks.
The Vulnerability of Standard NAS Storage
Legacy backup architectures often rely on standard file-sharing protocols like SMB or NFS to transfer data from primary servers to secondary backup targets. While efficient for data availability, this approach exposes NAS Storage to the exact same risks as the primary network. If a threat actor compromises an administrative account, they can easily traverse the network, locate the attached backup volumes, and execute destructive payloads across both production and recovery environments simultaneously.
The Mechanics of Network Share Compromise
Modern ransomware variants are programmed to actively search for connected network drives, unmapped shares, and hidden administrative volumes. Once NAS Storage is discovered, the malware attempts to leverage compromised credentials or unpatched protocol vulnerabilities to gain write access. Because traditional backup appliances often prioritize high-speed data ingestion over strict logical isolation, they present a highly lucrative target.
To mitigate this systemic vulnerability, IT departments must transition toward purpose-built NAS solutions that incorporate hardware-enforced security protocols and strict zero-trust network access (ZTNA) frameworks.
Core Principles of Ransomware-Resilient NAS Solutions
Designing a backup environment capable of surviving a targeted attack requires layering multiple security controls to eliminate single points of failure. The architecture must assume that perimeter defenses will eventually be breached, placing the burden of protection directly on the storage medium itself.
Logical Isolation and Write-Once-Read-Many (WORM)
A resilient backup architecture fundamentally restricts how data is written and modified. WORM compliance ensures that once data is committed to the storage appliance, it cannot be altered, overwritten, or deleted by any user, including root administrators, until a predefined retention period expires. High-performance NAS solutions achieve this through proprietary file system controls that lock data blocks at the kernel level.
By integrating WORM protocols, administrators effectively remove the primary weapon of ransomware: unauthorized encryption. Even if an attacker gains full administrative access to the network, the underlying storage OS will reject any modification commands directed at the protected volumes.
Deploying Immutable Snapshots for NAS
The most critical component of a modern backup architecture is the utilization of Immutable Snapshots for NAS. Unlike standard storage snapshots, which can be deleted by administrators to free up capacity, an immutable snapshot is cryptographically locked. The system generates a read-only, point-in-time representation of the file system that is protected by a time-based retention lock.
When configuring Immutable Snapshots for NAS, engineers must ensure that the retention clock syncs with an external, tamper-proof time source. This prevents threat actors from manipulating the system time to prematurely expire the retention lock. By scheduling frequent Immutable Snapshots for NAS, organizations can establish a highly granular recovery point objective (RPO) without expanding their attack surface.
Architecting the Secure Data Vault
Building a ransomware-resilient infrastructure requires careful integration between the backup software application and the underlying storage hardware. The design must facilitate automated data protection while strictly limiting interactive access.
Optimizing NAS Storage Topologies
The physical and logical placement of NAS Storage dictates its survivability during a cyber incident. Best practices dictate isolating the backup storage on a dedicated, non-routable VLAN. Traffic should only be permitted between the backup application servers and the storage appliance via strictly defined firewall rules.
Furthermore, management interfaces for the NAS Storage must be entirely separated from the data plane. Access to the administrative console should require multi-factor authentication (MFA) and originate strictly from a secure jump server or privileged access workstation (PAW). This segmentation ensures that a compromise of the general corporate network does not grant a pathway to the storage management layer.
Retention Strategies for Immutable Snapshots for NAS
Storage capacity planning becomes highly complex when implementing immutability. Because locked data cannot be deleted to reclaim space, administrators must carefully calculate the required storage footprint based on the change rate of the production data and the duration of the retention policy.
A standard architectural pattern involves maintaining short-term Immutable Snapshots for NAS on high-performance flash storage for rapid recovery, while tiering older locked snapshots to dense, cost-effective magnetic storage or immutable cloud buckets. This tiered approach balances rapid recovery time objectives (RTO) with sustainable infrastructure costs. It is vital to periodically review these policies to ensure that the retention locks align with current compliance mandates and business continuity requirements.
Operational Security for NAS Solutions
Technology alone cannot secure an environment. The deployment of enterprise-grade NAS solutions must be paired with rigorous operational security protocols to maintain the integrity of the data vault over time.
Role-Based Access Control and Multi-Person Authorization
Administrative access to the backup infrastructure must operate on the principle of least privilege. Comprehensive NAS storage solutions support granular role-based access control (RBAC), allowing organizations to separate backup operational duties from storage administrative duties.
To defend against insider threats and compromised root accounts, advanced platforms implement multi-person authorization (often referred to as a "four-eyes" principle). Any critical operation, such as altering global retention policies or upgrading firmware on the storage appliance, requires cryptographic approval from at least two distinct authorized administrators. This administrative friction is highly effective at stopping automated malicious scripts and rogue actors.
API Security and Automation
Modern data centers rely heavily on automation to manage infrastructure at scale. However, unsecured APIs present a massive risk to backup environments. When evaluating different NAS solutions, security architects must verify that all REST APIs require secure token-based authentication and support comprehensive audit logging. Automation scripts that interact with the backup environment must utilize secure credential vaults rather than hardcoded passwords to prevent credential harvesting.
Securing the Future of Enterprise Data
Ransomware operators will continue to refine their methodologies, seeking new vectors to exploit enterprise networks. Relying on perimeter security and standard replication protocols is no longer sufficient to guarantee data survival. Organizations must adopt an assume-breach mentality, engineering their data protection workflows to withstand direct, privileged attacks.
By hardening network topologies, enforcing strict access controls, and leveraging hardware-enforced immutability, systems administrators can construct an unassailable data vault. The rigorous application of these architectural principles guarantees that critical business data remains pristine, providing a definitive path to recovery regardless of the threat landscape.